In the previous part, we have gone through computer networking protocols and topologies. In this part, we will discuss the network structure, which is the OSI model and TCP/IP model. So let's get started.
OSI MODEL (Open System Interconnection Model)
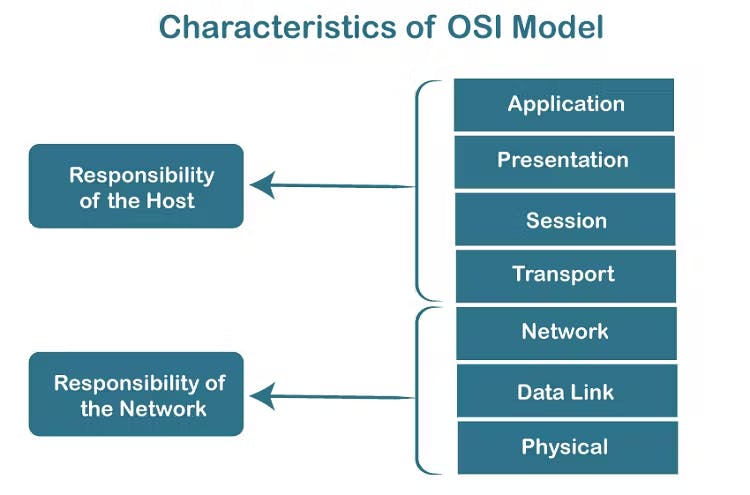
There are 7 layers in OSI model and they are:-
Application Layer | Implemented in Software |
Presentation Layer | It converts those messages, and data into machine-representable binary format. |
Session Layer | Helps in setting up and managing the connections and enables sending and receiving of data followed by the termination of the connected session. |
Transport Layer | Data received from the session layer is divided into small data units called segments. |
Network Layer | The transmission of the received data segments from one computer to another that is located in a different network. |
Datalink Layer | Physical addressing is done here Mac addresses are called physical addresses. |
Physical Layer | It contains all the hardware kinds of stuff like cables and wires. |
What is MAC address - MAC address stands for Media Access Control Address.
It is a 12-digit alphanumeric number or a hexadecimal number of the network interface of the computer network layer.
Application Layer
This is the layer that provides service to the user basically users interact with it.
It consists of application software like web browsers and chat applications.
This layer provides services to the user.
This layer includes all high-level protocols like Telnet, DNS, HTTP, FTP, SMTP, etc.
Presentation Layer
The presentation layer converts the data into machine-representable binary format Extended binary coded decimal interchange code translation.
It provides data abstraction, thereby giving the necessary information.
It provides encryption/decryption. Which uses SSL protocol to encrypt data.
It compresses data so that it can travel long distances without any frame drop.
Session Layer
A session is a logical connection between two applications to have multiple interactions.
It helps in setting up and managing connections.
It enables the sending and receiving of data followed by the termination of connective data.
Authentication and authorization take place here. First, it asks for credentials for authentication then it does authorization whether you have access to the server or not.
Transport Layer
It is responsible for error-free and end-to-end delivery of data.
The protocols defined here are TCP ( Transmission Control Protocol ) and UDP ( User Datagram Protocol ).
TCP is the connection-oriented transmission ( eg: email)
UDP is the connectionless oriented transmission ( eg: Videocall)
The transport layer does the following tasks to ensure that the data reaches its destination.
Segmentation - Data received from the session layer is divided into smaller segments. Every segment will contain a source port number, a destination port number, and a sequence number. The sequence number helps to reassemble the sequence of segments in the correct order.
Connection management - It uses TCP and UDP for transporting the data segments.
Network Layer
It is responsible for moving the data packets from the source to the destination.
It uses the IP (Internet Protocol) for distributing data packets through the network.
Functions of the network layer:-
Logical Addressing: The IP addressing done in this layer is called logical addressing. This layer assigns the sender's and the receiver's IP address to every segment and it forms an IP packet. It's in this way that every packet can reach its correct destination.
Performs routing: It moves the data packets from source to destination using the shortest path available. One of the algorithms used is Dijkstra's algorithm.
Load balancing: This layer makes sure that the data is not overloaded over the network.
Datalink Layer
The data unit in the Datalink layer is called a frame.
The data link layer is responsible for the error-free transfer of data frames.
It performs physical addressing. Meaning, the data link layer encodes the source and destination's MAC address/physical address in the header of each frame.
It helps to synchronize the data flow speed between the sender and the receiver.
Functions of Datalink Layer-
Flow control - The layer manages the flow of data between the sender and the receiver to avoid congestion. For example, a server sends data at a speed of 60 Mbps and a client receives the data at a speed of 30 Mbps. Here we can see that there is a speed mismatch that won't work. This layer takes care of it.
Error control - This layer detects and transmits any lost or corrupted segments to ensure reliable delivery of data. To check whether the data is corrupted or not, it adds a checksum to every data segment.
A checksum is a value that is calculated from a block of data using an algorithm like CRC-32, MDS, SHA-1, etc.
Physical Layer
The physical layer provides a physical medium through which bits are transmitted.
The physical layer contains information in the form of bits.
The data rate is maintained by the Physical Layer.
It is responsible for the actual physical connection between the devices.
Protocols
Network protocols are a set of rules outlining how connected devices communicate across a network to exchange information easily and safely.
Examples
HTTP -> (Hyper Text Transfer Protocol)
DHCP -> (Dynamic Host Control Protocol)
FTP -> (File Transfer Protocol)
SMTP -> (Simple Mail Transfer Protocol)
POP3 -> (Post Office Protocol)
IMAP -> (Internet Message Access Protocol)
SSH -> (Secure Shell)
VNC -> (Virtual Network Computing)
Data are called by different names at different layers:
Transport layer -> Segments
Network layer -> Packets
Data link layer -> Frames
Status Code
Every request has a status code which is used to know the status of that request,
1 x x -> Information
2 x x -> Success
3 x x -> Redirecting
4 x x -> Client error
5 x x -> Server error
Conclusion
Thank you for taking the time to read my blog! I hope you found the information about computer networking which is an essential system that enables devices to exchange information and resources. The OSI model provides a framework for understanding network communication, dividing it into distinct layers. Understanding the OSI model and protocols is vital for building and maintaining reliable networks, ensuring effective communication and troubleshooting capabilities.
Your interest and support mean a lot to me. If you have any further questions or topics you'd like me to cover in the future, please feel free to reach out. Stay connected and stay curious!
